Drive Efficiency With Centralized IT Assets, Automated Risk Scoring, & Project Management. Built by ITRC Experts to Meet Your Exact Needs. Enable Org-Wide Collaboration & Adoption A security risk assessment is a process that helps organizations identify, analyze, and implement security controls in the workplace. It prevents vulnerabilities and threats from infiltrating the organization and protects physical and informational assets from unauthorized users. Requirements

Security Assessment Template 18+ (Word, Excel & PDF Format)
An application security risk assessment is a process of identifying, assessing, and managing the potential risks to an application. Not only does this help prevent the exposure of security defects and vulnerabilities, but it also helps you see your app through the eyes of cyber criminals and attackers. Application security risk assessment checklists can help organizations determine which areas of their application environment need additional protection or attention to ensure that their systems remain secure from malicious actors. Every application is unique and carries threat factors. This guideline is consistent with the requirements of the Office of Management and Budget (OMB) Circular A-130, Section 8b(3), Securing Agency Information Systems, as analyzed in Circular A-130, Appendix IV: Analysis of Key Sections. The NIST Risk Management Framework (RMF) provides a comprehensive, flexible, repeatable, and measurable 7-step process that any organization can use to manage information security and privacy risk for organizations and systems and links to a suite of NIST standards and guidelines to support implementation of risk management programs to meet the requirements of the Federal Information Security.

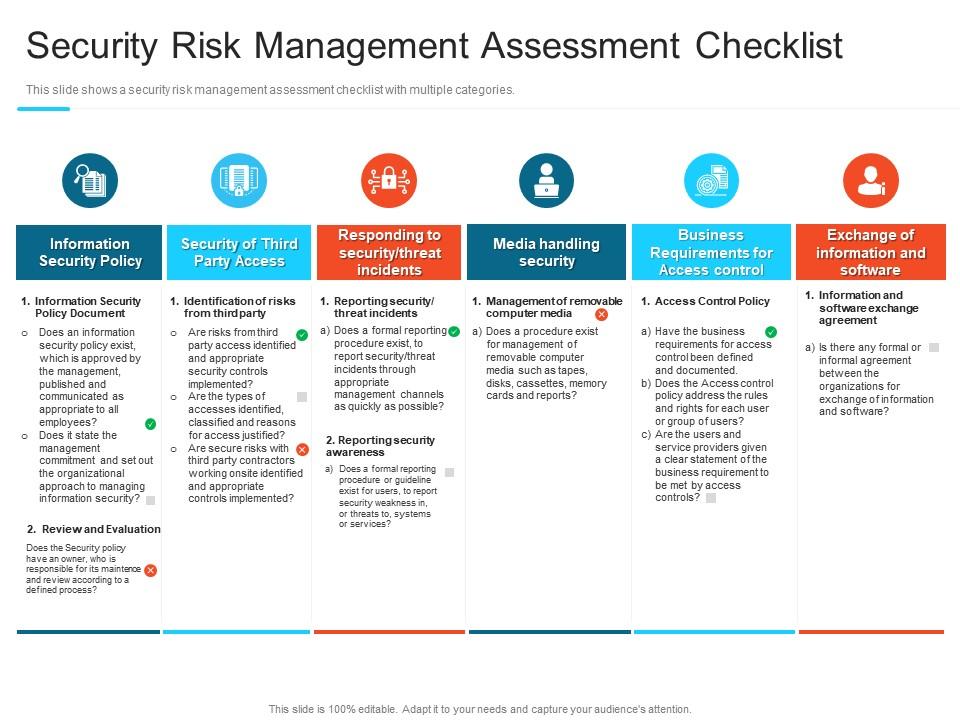
Security Risk Assessment Checklist Template
Step 3: Analyze risks and determine potential impact. Now it is time to determine the likelihood of the risk scenarios documented in Step 2 actually occurring, and the impact on the organization if it did happen. In a cybersecurity risk assessment, risk likelihood -- the probability that a given threat is capable of exploiting a given. What is Security Risk Assessment? Security risk assessment is performed to allow organizations identify and assess security posture. The assessment's primary purpose is to inform decision-makers about the security risks that might surface in the organization and ease risk handling. This information security risk assessment template includes a column for ISO 27001, so you can apply any of the International Organization for Standardization's (ISO's) 14 information security standards steps to each of your cybersecurity risks.. Use this cybersecurity risk assessment checklist template to meet your cybersecurity goals. Using a cyber security risk assessment checklist can help you understand your risks and strategically enhance your procedures, processes and technologies to reduce the chances of financial loss. This document explains the key elements of an effective checklist. Checklist: Essential Elements of a Security Risk Assessment
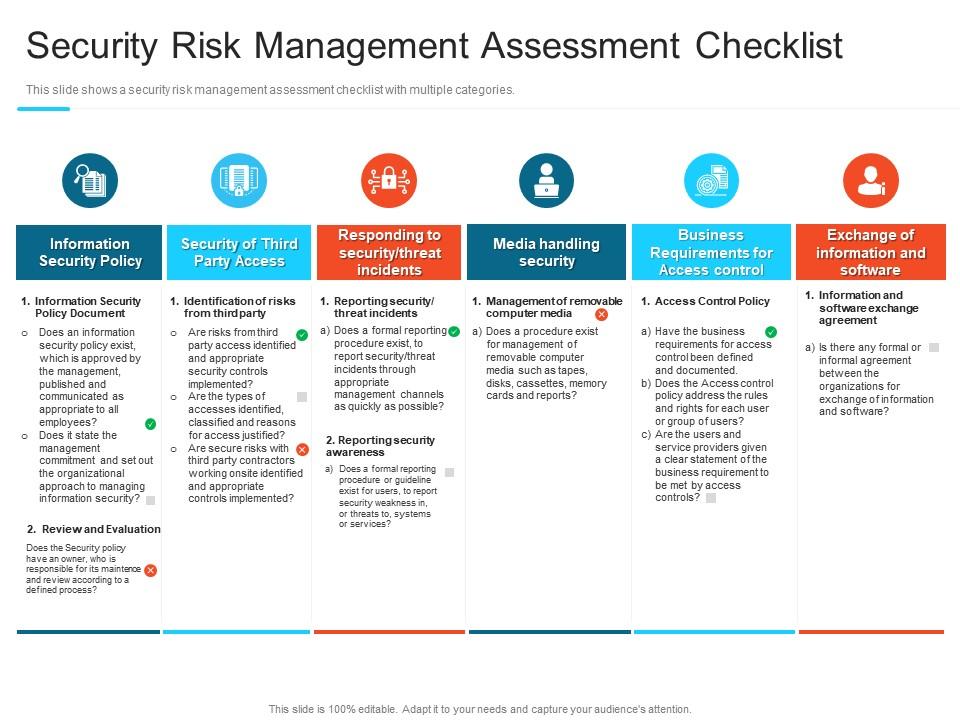
Security Risk Management Assessment Checklist Steps Set Up Advanced Security Management Plan
A security risk assessment should be performed annually, if not quarterly. Consider using a checklist — such as the xlsx file from TechRepublic Premium — to not only coordinate security. The first step in a security risk assessment process is to define the scope. For a HIPAA security risk assessment, this means to catalog all your information assets that store, use, or transmit electronic protected health information (ePHI). Next, identify the security controls in place.
Security assessments have specific objectives, acceptable levels of risk, and available resources. Because no individual technique provides a comprehensive picture of an organization's security when executed alone, organizations should use a combination of techniques. Now that you know what you should gain, let's go over the eight steps involved with our cyber security risk assessment checklist: 1. Identify the high-value assets across your organization that could be impacted by threats. Common examples include servers, domains, trade secrets, customer credit card data, and other sensitive client information.

Business Risk assessment Template New 10 Sample Security Risk assessment Templates Pdf Word
This publication provides a methodology and set of procedures for conducting assessments of security and privacy controls employed within systems and organizations within an effective risk management framework. A security audit checklist is a comprehensive tool used to assess the security measures and controls in an organization's systems, processes, and infrastructure.